The SecretPi – The secret agent privacy guard for Managers, Reporters, Dissidents and People like you and me, keeps nosy people out.
The Motivation (How the SecretPi came to be)
 |
|
 |
Whilst creating a Raspberry Pi3B for a friend in Turkey, who want’s to watch German TV programs over the internet and do not want to have the Government monitoring his behaviour (mail, browsing etc.), an idea came to my mind. As my friend only needs a VPN which is maintained by the Raspberry and automatically starts where ever / when ever he is connected to the internet via his DSL Router, I started thinking about people who need more than just a VPN.
Actually – and due to the current (2018) situation in Turkey, Syria, Mali and many other countries – I was specifically thinking about:
- Reporters of all kind
- Editors
- Writers
- Dissidents
- People who have to hide
- NGO people
- Groups or organisations
- Whistleblowers
Because these people and their contacts, are very often in danger and need strong protection when using the internet.
In another sleepless night, I found another group of people who are in need of such a device:
- Managers or other important persons of a company which is targeted by industrial espionage, especially when they travel abroad
- Small offices of companies, targeted by industrial espionage, residing in “evil” countries or environments
- Expats living in foreign countries, but would like to overcome “geoblocking” of streaming sites, newspapers, tv and radio
- Anyone who wants to protect their privacy
- Anyone who travels abroad
With other simple words: WE ALL NEED TO PROTECT OUR PRIVACY !
If you want to know more about the SecretPi, click here to get the flyer !
The knowledge and experience behind
Please keep in mind that I have a career behind me, where I was somehow “on the other side”. I was medium range sniper in the German army in an anti-sabotage-protection group during my service, have consulted and trained government organisations (like…and similar to CIA, FBI, state police and secret service) in many countries in the world for lawful interception, communication behaviour analysis, graphical analysis, text analysis with n-gram algorithms and the visualisation of data. I was actually trained by retired NSA Agents in the US for visualising data. This may scare you, but honestly I was never involved in real actions on data or people, I always used my clean set of demo data. The aim of my trainings was to fight organised crime and terrorism as I started directly after 9/11, and I also like to keep my data and communication under privacy and btw. I have lived also in countries which are still “difficult”.
But knowing “the other side” has a big advantage. I know how and what they can do and can estimate what is technically possible today to harvest information from people, groups or organisations. Therefor I can use my knowledge to make data really private and protect endangered persons, groups or organisations.
The scenarios
 Living myself in a kingdom which is known for it’s conservative interpretation of the Quran, I was part of a oppressed society. Especially when it comes to what can happen and how to protect yourself from evil actions of the government, blocked internet connects and so on, I have learned my lesson. So the creation of some scenarios was easy:
Living myself in a kingdom which is known for it’s conservative interpretation of the Quran, I was part of a oppressed society. Especially when it comes to what can happen and how to protect yourself from evil actions of the government, blocked internet connects and so on, I have learned my lesson. So the creation of some scenarios was easy:
- Your communication should not be monitored (intercepted)
- Websites should be freely available not blocked or geoblocked
- You want / have to keep your communication secret and encrypted
- You want/have to hide your whereabout
- Authorities may come to your house and seize your computers and other equipment necessary for investigation
- You get jailed and questioned about your usernames and passwords
- The Authorities investigate and analyse your data
- The hacker department infects your PC with a trojan horse to intercept
- If your data is analysed, you may bring other people in danger
- If you have to disappear (to run) you have to take your data with you, inconspiuous, light weight.
- Physical data (disks, SD cards) must be inconspicuous send by courier or post to a safe harbour
- When you communicate you appear as if in another country
- Your equipment must have a self-destroy mechanism (booby-trap)
- Your physical data volumes can not be run on normal computers
- The equipment must be small, portable and can be operated even on batteries
- The battery must act as UPS (Uninterruptable Power Supply) in areas where power-glitches or -interruptions are common
- To confuse the people who want to harm you, it can be build into curious “housings” not looking like a computer
- It must work with LAN and WLAN to connect to the outside (Internet) and offers LAN and WLAN to the inside
- Autonomous use, the device itself must have capabilities like a small office PC with office applications and the ability to chat / transfer files securely
Well, that was a hell of topics to solve !! – But I did it !!
The solution (and for which scenarios)
After some more sleepless nights, I started the project on a raspberry pi 3B based on the solution for my friend in Turkey, with a VPN. Than I added a lot of stuff:
Boobytrapped, encrypted filesystem
First of all I implemented an encrypted filesystem which requires a username and password, once activated. If you enter the password several times (definable) wrong, the filesystem destroys itself. Also there is a destroy-user implemented which – when typed in – destroys the filesystem just by the first attempt. This takes care of tampering with the device from a unauthorised person, which tries to guess username and password. Also it takes care if you are arrested and questioned (but your life is not in danger when you fool the interrogator) to use the boobytrap-user to destroy the filesystem. With a function described later the data will be also destroyed, if the SD-card is used on a RaspberryPi, without SecretPi functions. Even if the SD-card is removed from the device and is analysed by the use of a forensic workstation (the boobytrap will not work than), it is encrypted, not easy to make the content visible. This protects you and other people you have communicated with.
VPN for encrypted data transfer
The build in VPN (which is compatible to managed VPN providers like nordvpn, hide-my-ass and others) makes sure that everything what comes out of the SecretPi (towards the internet) is encrypted, furthermore you can decide in which country the endpoint of the VPN connection is, that means where you come out of the “tunnel”. This is used to make it look like you are somewhere else and the data in transit can not be read in clear text. Furthermore it is extremely hard to find the IP-Address of the origin of the data geographically. BTW: If you use the SecretPi as a router and you have your network behind the SecretPi, no one is stopping you from using another VPN or encryption mechanism on your home devices like Laptop, PC, Smartphone or Tablet. Than you will encrypt at least twice VPN wise (tunnel in tunnel setup).
Applications support multi-level-encryption on the SecretPi
The SecretPi is designed for multi-level-encryption when it is used autonomous as a kind of PC. That means a set of data can be encrypted multiple times. The VPN encrypts the data transmitted, with the Nautilus GnuPG File-Manager you encrypt a file manually and send it by Telegram desktop, where it is encrypted again. This gives you 3 different encryptions. Do not forget to give difficult (hard to get by by bruteforce or guessing) passwords in each step or technology used.
Small device, easy to hide and transport (can also be build in curious housings of all kind)
As a RaspberryPi housing is quite small, it can easily been hidden. Also I can build it into any kind of housings, glue it under the table or whatever comes to your and my imagination to let it disappear or being visible, without looking like a RaspberryPi. Even the argument, “but there is always at least one cable” can be eliminated, as it can be run in complete wireless mode and can be powered by a power-bank (USB rechargeable battery).
SecretPi is always in “Stealth” mode
The SecretPi was hardened that it will not answer to any requests from the outside and it is invisible to probing (LAN/WLAN connection to the outside only). This was done by specific firewall settings on the SecretPi and it was tested with professional equipment and human penetration testing. This makes sure that the SecretPi can not be discovered by active scans in the network, but the existence of the SecretPi can be discovered by sniffing the network-traffic.
Linux Environment protects from malware (trojan horse)
Actually it is hard to infect a Linux environment (the SecretPi runs on Raspian stretch) and updated to the latest release, it should be pretty safe to get not infected by malware (government use, or regular ones). That prevents together with the stealth mode, that the SecretPi can not be infected for interception or data-harvesting.
Autonomous use
The SecretPi was designed for autonomous use. That means you can use it as a standalone device, as it has useful applications “on board”. These applications are the OpenOffice Suite, Telegram Desktop, PGP for file-encryption, a VoIP client for phone calls, Nautilus GnuPG (a file manager to encrypt files or directories), Claws Mail, Teamviewer for remote access and Webmin (for some administrative tasks). If the SecretPi is used without having a LAN or WAN and/or no electric power for the USB adapter is available, you can run with the battery autonomous. That means you can write your articles, messages etc. but they are not send out directly (no internet in this scenario), but directly when you connect to the internet again.
Well, we had debates about Teamviewer as a remote access (support) tool, as it gives – as the name says – remote access, which by definition could be an ingress point to compromise the SecretPi. As good arguments won the battle the decision to use Teamviewer was made, as you cannot use Teamviewer without consent of the SecretPi user. Teamviewer creates each time a randomly generated password for the Teamviewer ID of the SecretPi, which has to be given to the other party. On the other hand it can be used (beside the support functionality) to give someone a look at your device (just the screen is being transferred, which is a safety aspect), files can be transferred etc., in a kind of OOB (out of band) communication, still through the VPN.
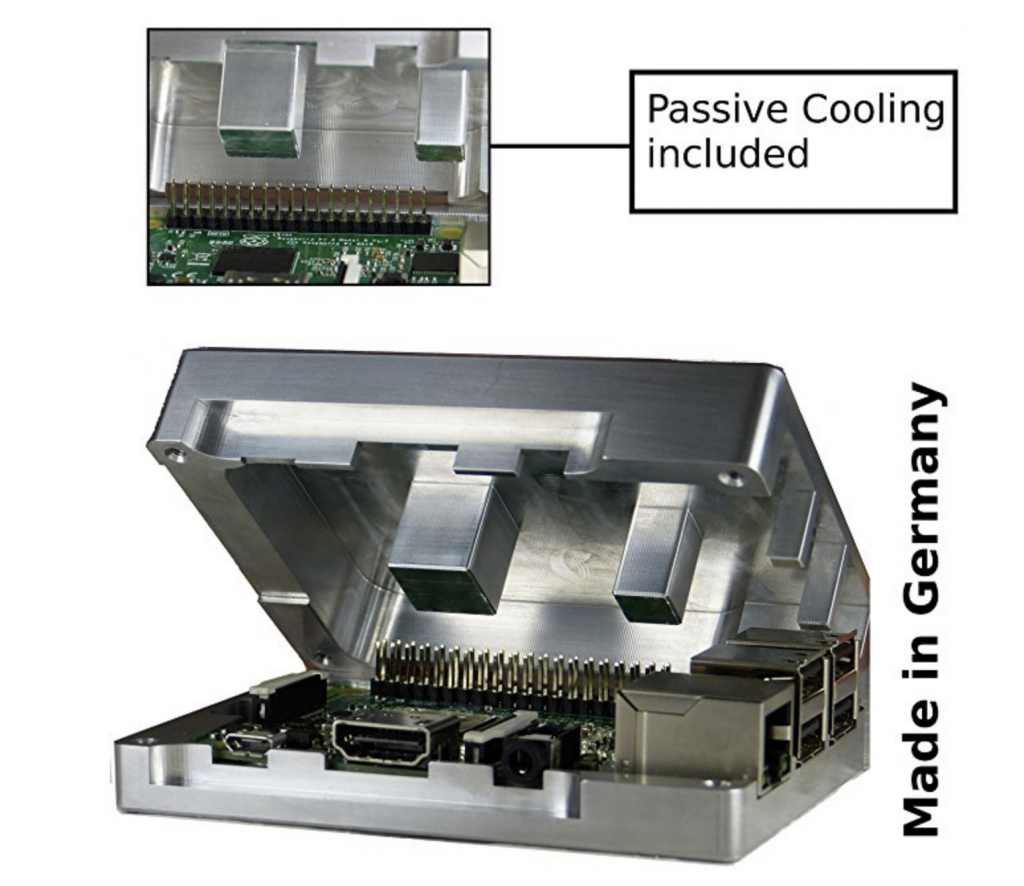
Rugged version for evil environments
A special edition of the SecretPi comes in a rugged version. A full metal housing (aluminium) which acts as a heat sink for the raspberry pi processors, nearly undestroyable for the use in areas where IED’s (Improvised explosive devices) are common, explosives (bombs, grenades, RPG’s (hand-held antitank grenade launcher), etc., are used or other physical stress can affect the device. Right now, there is no waterproof version available (maybe after another sleepless night), at least it comes with a waterproof peli-case for transport and storage. This kit is designed for war-like or disaster environments. Of course, the battery can be used also with this housing, if there is no electric power available. Beside the housing the facts about SD-cards environmental tolerances are very impressive.
Just take the data with you (The “I have to run” scenario)
Imagine, authorities knock your door and you know what happens next. You have only a very limited time to hide things. Just quickly remove the SD-card and hide it on your body, in one of your socks, in your shoe, in your mouth (SD-cards can stand humidity see here). This can be done in no time. Basically there is no limit where you can hide it, as a micro SD’s are very small. Alternatively you can hide it with a piece of double sided tape anywhere, by just sticking the SD-card to the tape and leave it on premises.
Boobytrapped device, only available to it’s owner
Imagine, someone breaks into your house to take your SecretPi. But “someone” will not be very happy, as I have bound the SecretPi to you and the SecretPi will only start properly if you are around at boot-time. The trick is a NFC (near field communication) device. This can be a credit card style NFC card, a ring (Yes…a NFC Ring for your finger with a build in transponder), a generic NFC transponder which can be glued to anything (i.e. a vase or a box of matches laying/standing on the SecretPi), or even false nails containing a NFC transponder (Ladies listen !). The SecretPi NFC boobytrap expects it’s corresponding NFC transponder at startup. If it can not find it, it will display a fake message like “System was updated, please switch off and on again to boot”. Well, this message is a hoax for those people who do not have the right transponder and have no clue that it is needed to deactivate this boobytrap, cause they do not even know that there is a boobytrap. If the system is started again, it will say “Update completed and verified, booting in 30s” with a countdown. If the “right” transponder is not there within 30s, the system will destroy itself. Well, it will not go onto fire (maybe I should sleep over it), but everything on the SD-card will be wiped, not only the encrypted file-system, but the whole SD-card content.
Uninterruptible Power-Supply
If you are in an area with power-glitches, frequent power-loss, or non solid voltage or frequency, simply connect the USB-Power Adapter to the Power-Bank for charging and the USB-Power output of the Powerbank to the SecretPi. Now you are safe against power-failures. Make sure, that the power on/off switch is between the Powerbank and the SecretPi, that you can switch it on or off.
Future Enhancements
Currently I plan to have some more sleepless nights, as I want to make the SecretPi independent of WLAN or LAN Access Points. In the future I want to teach the SecretPi to use also other communication networks; like Satellites, HAM Radio or whatever comes to my mind for OOB Communication. That will make the SecretPi more versatile in hostile environments, where no Internet and electric power is available and also helps to obfuscate data traffic. On top, some managed services are planned which could extend this project to make things even more safe. Stay tuned.

Isn’t it exiting – a RaspberryPi which could even be an addition to James Bond’s arsenal ?
How can you get a SecretPi ?
If you want to know more about the SecretPi, click here to get the flyer !
First of all we have planned to bring the actual prototype finalized and ASAP to the market, just the funding for going from prototype to production has to be done. The SecretPi will come in the following configurations:
|
|
The “Dissident”-Version:
- Raspberry Pi 3B in the standard housing with cooling fan
- 64 GByte SD-card
- USB Power Adapter (stronger than most of the standard ones) with on/off switch, with international power-plug adapter (exchangeable)
- WLAN USB Adapter for the internal wireless network
- LAN USB Adapter for the internal wired network
- USB Powerbank with >12.000 mAH capacity
- Car USB Power Adapter
- 1x NFC-Ring, 1x NFC Card
- Watertight, crushproof, and dustproof Peli-Case, for safe transport and storage
- Quick Start Manual (English/German)
- Unlimited Access to the User-Forum
- Unlimited Access to the Support-Area
- 1 year Telephone and remote access Support (renewable)
- Individual configuration to your needs
- 2 years free Updates and Upgrades
The “Home Use” Version:
- Raspberry Pi 3B in the standard housing with cooling fan
- 64 GByte SD-card
- USB Power Adapter (stronger than most of the standard ones) with on/off switch, with international power-plug adapters (exchangeable)
- WLAN USB Adapter for the internal wireless network
- LAN USB Adapter for the internal wired network
- 1x NFC-Ring, 1x NFC Card
- Quick Start Manual (English/German)
- Unlimited Access to the User-Forum
- Unlimited Access to the Support-Area
- 1 year Telephone and remote access Support (renewable)
- Individual configuration to your needs
- 2 years free Updates and Upgrades
The “War Reporter” Version:
- Raspberry Pi 3B in a rugged housing without cooling fan (housing is the heat sink)
- 64 GByte SD-card
- USB Power Adapter (stronger than most of the standard ones) with on/off switch, with international power-plug adapters (exchangeable)
- WLAN USB Adapter for the internal wireless network
- LAN USB Adapter for the internal wired network
- USB Powerbank with >12.000 mAH capacity
- Car USB Power Adapter
- 1x NFC-Ring, 1x NFC Card
- Watertight, crushproof, and dustproof Peli-Case, for safe transport and storage
- Quick Start Manual (English/German)
- Unlimited Access to the User-Forum
- Unlimited Access to the Support-Area
- 1 year Telephone and remote access Support (renewable)
- Individual configuration to your needs (for groups, not single units)
- 2 years free Updates and Upgrades
Your specific Version:
- Upon request of specific groups (i.e. NGO’s or other Organisations which need specific configurations) we will create special Versions and/or kit’s to your needs, ask for details via the contact form.
- Also if you need a SecretPi, hidden by a curious housing or built into whatever, ask for details via the contact form.
- You have special ideas in mind, tell us via the contact form. We will try to make it happen.
Additional Information:
Prices will be subject to TBD, shipping costs and taxes are subject to the country of delivery.
Backers will get a substantial discount on the product and services which will make them breathless.
Want to become a backer, tester or investor ?
Welcome, the SecretPi Idea is currently looking for backers and investors. Most of the important stuff is already done, a prototype without boobytraps exists and runs like a charm and never drops the connection. We reach an encrypted throughput of up to 80Mbit/s on a 100Mbit/s DSL Connection. Now it is time to bring the SecretPi to the market. Some more development, testing and programming has to be done, but it’s already documented. What this project needs are backers and investors. The marketing has already started. The first announcement is this blog-entry.
Where to go to become part of the crowdfunding as a backer ?
This is not decided yet, which crowdfunding platform(s) will be our partner. More information will be released soon.
How to become a tester ?
Testers will get a device if they are a backer, with an even higher discount, if they test the device and send us their findings and report errors or other problems. As soon as the first financing round is done, we will call all backers, to become also testers. How we will do that, will be announced shortly after the financing took place.
How to become an investor ?
Just use the contact form in the top right menu or THIS link
How the SecretPi can be used in real life scenario’s and in different infrastructures
Home Use
In home use you ideally connect the SecretPi by cable (WLAN will also work) to your Internet connection (mostly DSL-Router). You can now use the SecretPi as a privacy router, connecting your devices to the internal WLAN or with the USB/LAN adapter. When using the LAN-Adapter, you should keep in mind that if you want to use multiple devices, you have to use a switch. Dual use (WLAN and LAN) is also possible. The SecretPi also accepts WLAN hotspots like smartphones in tethering mode.
Autonomous Use
If you have no internet, you can use the SecretPi as your office as office applications (OpenOffice) are on the SecretPi already installed. If you have no electric power, but you bought the “Dissident” version, you have the power-bank and 12V car-adapter to connect to a remaining source.
Dissident Use
You can use the SecretPi as described under “Home Use” and “Autonomous Mode”
Manager abroad use
You can use the SecretPi as described under “Home Use”,”Autonomous Mode” and “Hotel Use”
Small Office in foreign country use
See Home Use
Hostile Environment Use
You need the “War Reporter Version” with the rugged housing. Technically look at “Home Use” and “Autonomous Use”
Hotel Use
In a hotel or similar environment (i.e. Guest access in a company you visit), you connect the Secret Pi with the LAN to the hotels internet-connection or you use your smartphone in tethering mode or a portable access point. The SecretPi can not connect to a hotel or similar WLAN’s (guest networks), if the WLAN is open and the authentication to the network is done via an authentication window in the browser. The SecretPi is in stealth mode and will not see the authentication screen in the browser – Never, Ever !
Disclaimer
The SecretPi was tested over and over again, every trick and technology I could get hold of was used to find loopholes. There are to my knowledge none. But I do not take any responsibility and can not guarantee that data can/will be intercepted, decrypted and analysed against you. Please keep that in mind.









Recent Comments